Table of Content
Hackers are abusing the open-source Linux PRoot utility in BYOF assaults to supply a consistent repository of malicious tools that work on many Linux distributions. At Tableau, we discover thrilling information about information, analytics, and visualizations every single day. Sharing that information by way of our weblog is a key a part of our mission to assist people see and understand their data. From recommendations on using Tableau extra successfully to learning how on an everyday basis individuals are dealing with data challenges, the Tableau blog is a place for information lovers. Allowing customers to delete or replace their information at their desired cadence.
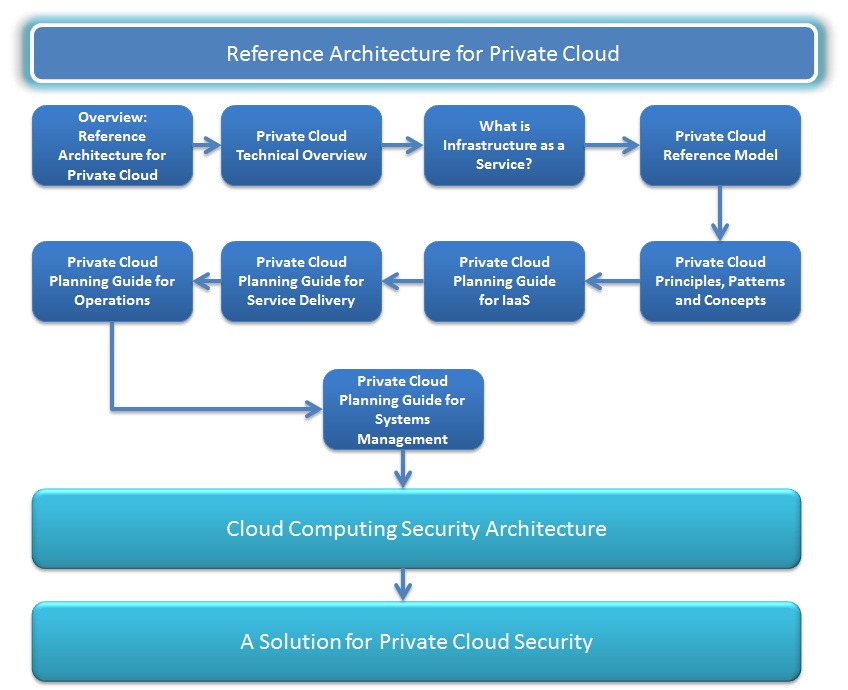
As its name implies, private clouds grant a enterprise non-public access to dedicated infrastructure sources within a cloud. As is the case for public cloud, there are both benefits and drawbacks with this infrastructure. A firm owns and operates the servers, or leases devoted servers from a datacenter. A personal cloud’s hardware may be stored on-site at a company’s property, or housed in a datacenter. In strictly regulated industries, such as finance and healthcare, a personal cloud is a compliance necessity. It is up to you to configure the cloud in a means that matches the wants of your business precisely.
What Are The Disadvantages Of Private Cloud?
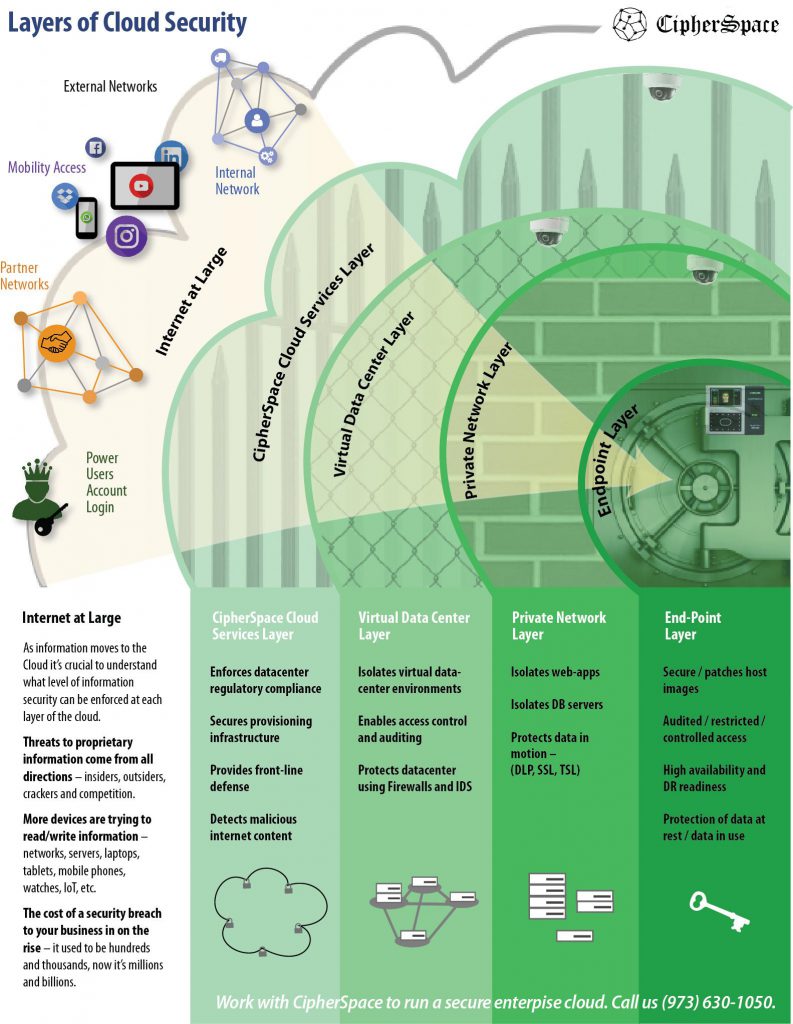
Cloud service suppliers only cover the safety of the cloud itself however don't protect customer information or using its infrastructure and purposes by customers. Security - your data and functions stay behind your firewall and are accessible only to your enterprise, making private clouds better suited to processing or storing delicate information. Choose your cloud enterprise companions with care; your small business will rely upon the provision of your cloud, whether or not it’s key knowledge or an software. The proper solution for your small business might not come from a single cloud supplier and it'll doubtless contain a community of partners across multi-cloud environments. Pairing your company’s cloud with a CDN provides access to a world network of cloud-based applied sciences. If there is a pure disaster in one space of the world, there are different servers ready and waiting to pick up the site visitors guaranteeing continuity of your web site or web-based purposes.
Also, embody regular safety consciousness drills for directors, developers, and end customers to tighten down your organization’s security posture. Access to the data heart is strictly monitored and solely authorized people can access servers. Use a menace detection system and log management to monitor access to your data and search for unfamiliar exercise, safety coverage violations, anomalies, or different malicious exercise. Services corresponding to Threat Stack Oversight might help with detecting threats in real time. This will either decrease your IT department’s available time for other duties or may require extra workers when internet hosting in-house.
Noc Management
Our award-winning community features virtualization solutions present our customers with unprecedented alternative and adaptability. Our ADVA Ensemble answer suite provides a complete NFV architecture that features programmable hardware, comprehensive software and end-to-end orchestration solutions. Scale and Segment the Cloud Rapid enterprise adoption of private and public clouds is driving the evolution of cloud security. Since the solutions lack complete network visibility and sometimes don't integrate collectively nicely, this could lead to gaps in safety and a weaker total safety posture. To meet the security challenges of hybrid cloud, enterprises want solutions designed with hybrid cloud in thoughts.

This contains sustaining information privateness and safety on online-based infrastructure, applications, and platforms. Protecting these methods involves the efforts of cloud suppliers and the shoppers who use them, whether they are utilized by individuals, small and medium businesses, or enterprises. With a public cloud, the IT staff will doubtless never see the bodily servers that house the company’s knowledge. In most cases, it’s difficult to know who will have entry to your servers (and the data that’s on these servers) on the datacenter. In the public cloud model, corporations pay for space and for what they use, and your company’s knowledge could probably be saved on the same server as other firms. For example, with public cloud infrastructure, enterprise IT doesn't have to worry about bodily safety at all.
Private Vs Public Cloud Security: Advantages And Drawbacks
Enterprises must choose between single- or multivendor SASE approaches, in addition to DIY or managed service choices. This history of enterprise wireless takes you from WLAN improvement contained in the enterprise to mobile data providers outside the ... Srovnejto.cz - Breaking the Legacy Monolith into Serverless Microservices in AWS CloudThe StormIT team helps Srovnejto.cz with the creation of the AWS Cloud infrastructure with serverless providers. Higher operational expenditure – as you scale performance it can be troublesome to manage your cost-per-hour. Governance - defining policies to manage costs and decrease security risks.
Enterprises can scale out or scale up with Fortinet FortiGate-VM virtual appliance offerings-virtualized versions of bodily community safety elements that deliver the identical capabilities as a bodily equipment in a virtual kind factor. FortiGate virtual firewalls deliver superior safety capabilities in a virtual form factor and are ideally suited to safe virtualized resources in the data center or personal cloud. Fortinet Security Fabric parts are all out there packages as digital home equipment on a broad vary of hypervisors. Due to the large scaling requirement that's anticipated in non-public cloud computing and cloud IaaS offerings, the necessity for highly powered servers turns into a strategic imperative. While UCS does not come low cost, it does provide flexibility and excessive service levels. In the long run, the total price of ownership of UCS ought to be considerably lower, particularly after factoring in decreased cabling, reminiscence, and labor prices that are derived from a fully virtualized, built-in administration infrastructure.
What Is Non-public Cloud Security?
Implement local and distant backup options similar to Acronis Cyber Backups. Also, make sure that backups are taken frequently, on a recurring schedule, and tested for performance. Finally, guarantee backups are on totally different mediums in order that if one fails or a backup becomes infected with malware, you have others to revive from. Referral Partner Program Build longstanding relationships with enterprise-level shoppers and develop your small business.
There are choices for businesses looking for increased safety whereas taking advantage of flexible public cloud infrastructure, such as a cloud-based content supply community. At CDNetworks, our cloud safety options provideDDoS protection, security for internet purposes and websites, and allow for the secure switch of information over the internet. As part of their private cloud structure, enterprise IT departments will usually use software program from providers like OpenStack, VMware, Cisco, and Microsoft to virtualize their datacenter. Users within the group – corresponding to particular person business models and staff – access assets like net applications and desktop services as wanted over a private community. When there is sensitive data to guard or data that comes underneath strict regulations, using a private cloud for security functions makes the most sense.
Security Ps Providers
For many security departments, this significantly reduces safety complexity from a uniformity point of view. For medium to massive enterprises, private clouds can provide economies of scale that makes the upfront capital investment worth it. For example, with private cloud, knowledge is controlled by and saved on servers owned by the enterprise, offering maximum management over access and data sovereignty. Further, non-public clouds allow enterprises to customize their infrastructure as required as opposed to being restricted by the offerings of a public cloud vendor. Virtual workload site visitors is logged and may be simply seen throughout the similar dashboard as bodily network logs. Organizations can employ third-party cloud service providers to handle purposes and knowledge within their information heart infrastructure.
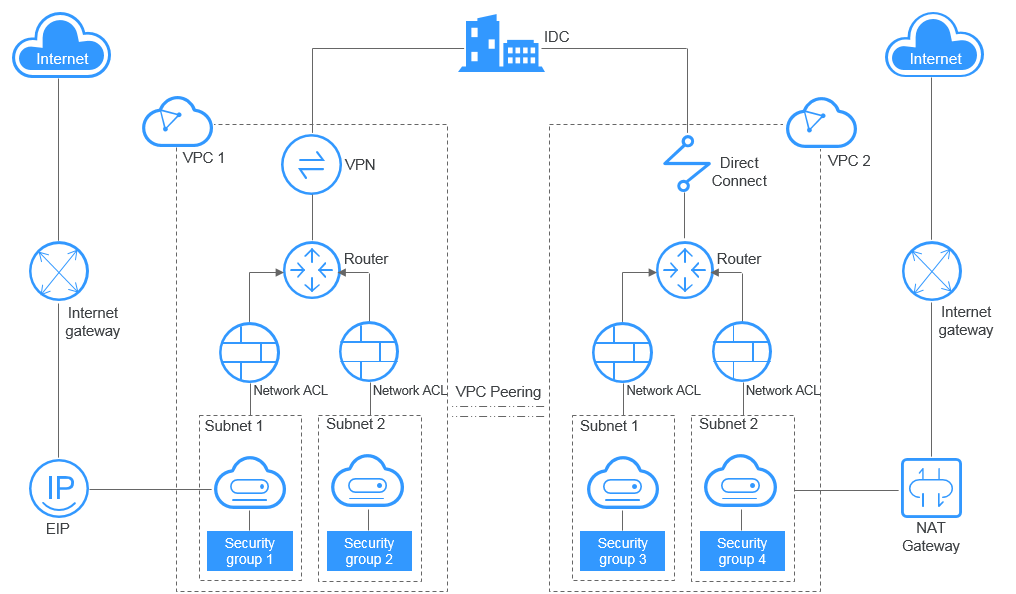
By the way, there are other worrying indicators that Anker’s safety practices may be much, much poorer than it has let on. This entire saga started when infosec advisor Moore started tweeting accusations that Eufy had violated different safety promises, together with uploading thumbnail images to the cloud without permission and failing to delete saved private knowledge. Anker reportedly admitted to the former, however known as it a misunderstanding. IPsec VPN and Mobile Access provide safe connectivity into cloud assets. Firewall, IPS, Antivirus and Anti-Bot protect providers from unauthorized access and attacks. In-house administrators have extra flexibility in relation to implementing and accessing security tools.
To satisfy clients, reputable public cloud suppliers normally spend more time on this area than any single organization to obtain this stage of reliability and security. Private cloud safety is an umbrella term that refers to the instruments and strategies used to secure non-public cloud infrastructure. Because sources are devoted to particular person enterprises, the personal cloud security paradigm differs from multi tenant public cloud environments. For example, there tends to be a giant increase in visitors between digital services, which isn't inspected or secured by conventional security methods. To enhance the confidence of CISOs and enterprise leaders, your cloud knowledge center needs a security technique and structure which may be designed in and inbuilt, not bolted on. Visibility and safety need to increase wherever the processes and information are.

No comments:
Post a Comment